What is the SURPRISE project about?
The SURPRISE project provides an advanced yet pragmatic approach for practical security and privacy (S&P) for smart environments: solutions that catalyse a broad set of applications and services, relying on well-understood and rigorously evaluated components that significantly advance the state of the art.
We tackle fundamental problems with far-reaching importance and relevance to potentially any smart environment.
Multi-University Project;
Trust management, including identity and credential management for S&P;
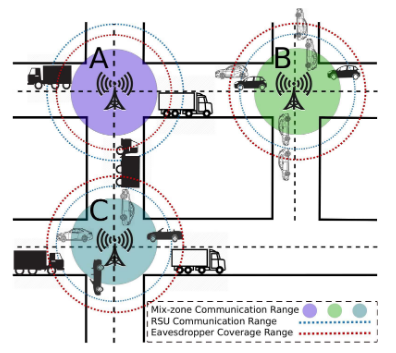
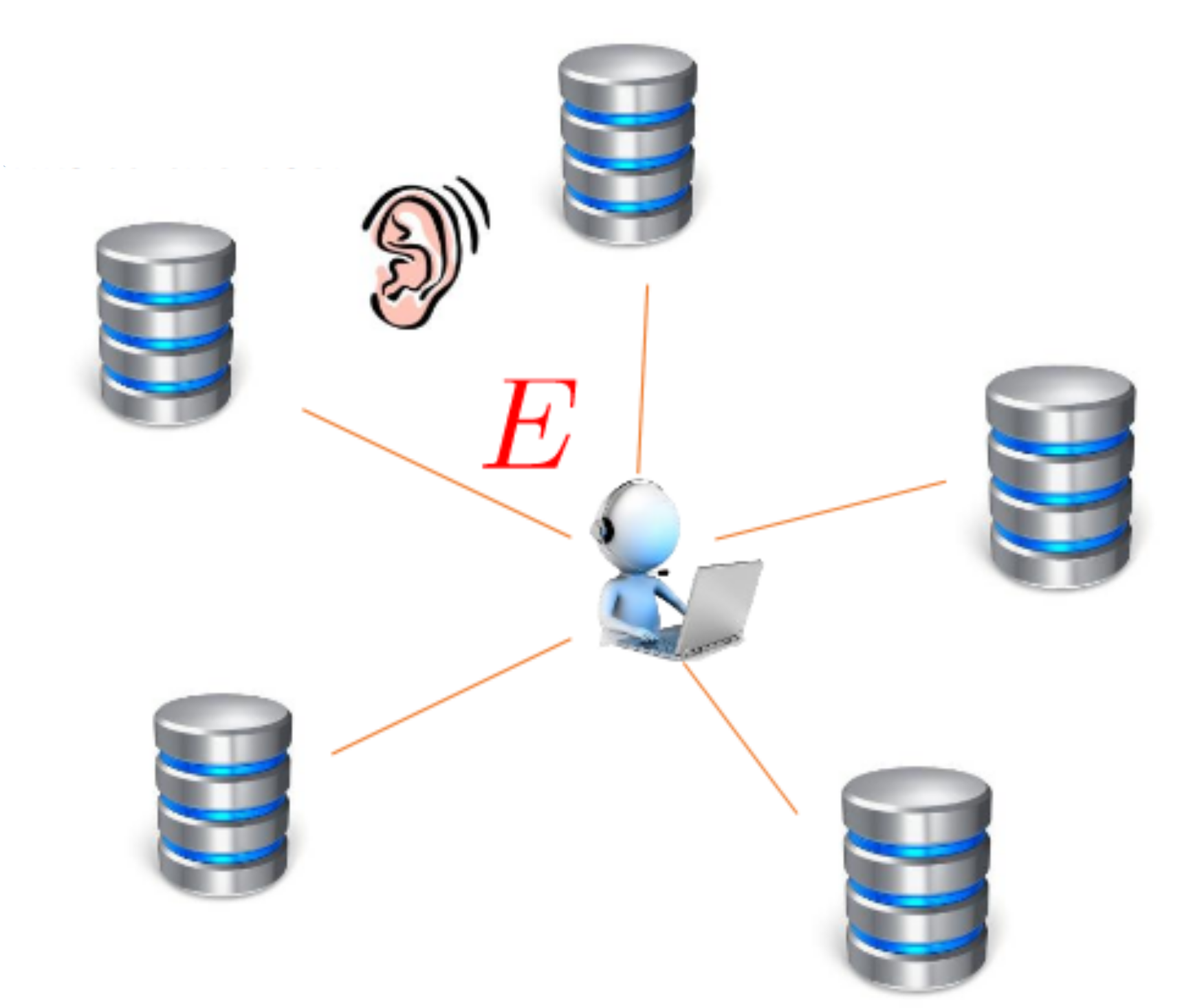
Lean, resilient S&P preserving communication and networking;
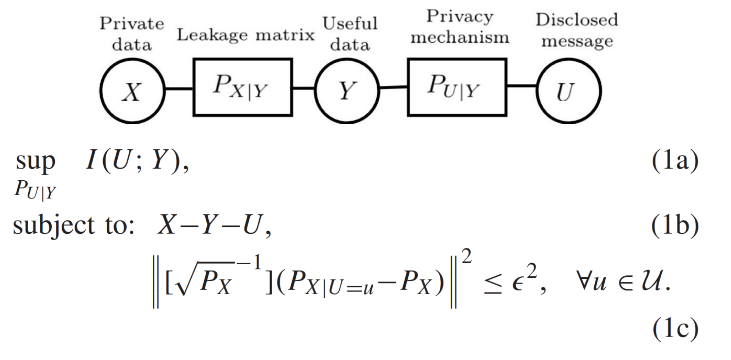
Data validation and S&P preserving processing
ScopeWe distill three key targets, three cornerstones of security and privacy for smart environments: trust management, lean and resilient communication, and data validation, storage, and analytics.
Read MoreGroupsThis multi-university initiative brings together five leading research groups at KTH, KAU, LiU and LTH.
Read MoreAdvisory BoardA diverse set of stakeholders are part of the Project Advisory Board, notably with rich representation of Swedish industry.
Read MoreHighlights
Below is a set of significant representative, across the project Work Packages, publications.
Research
About Us
Contact
For any query regarding the SSF-funded SURPRISE project, please contact Prof. P. Papadimitratos
For any query regarding the participating research groups, please contact the corresponding PI:
KTH-NSS: Prof. P. Papadimitratos
KTH-ISE: Prof. M. Skoglund
LiU: Prof. E. G. Larsson
LTH: Prof. T. Johansson
For any query regarding the website, please contact K. Kalogiannis
To find the Networked Systems Security group, please come to:
KTH Kista, Kistagången 16, Floor 4
Division of Communication Systems
Find us via map: 59°24'17.6"N 17°56'58.3"E